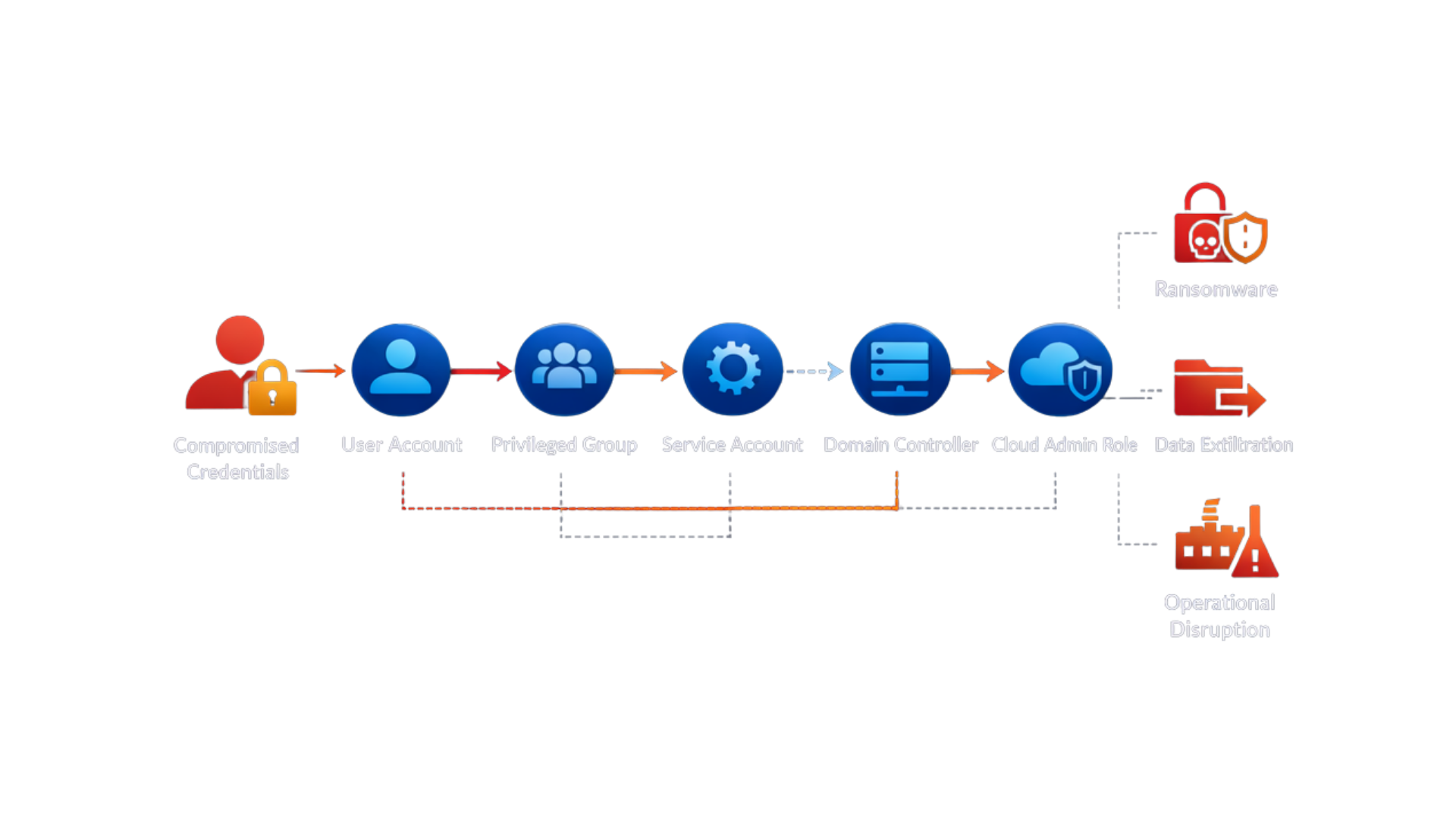
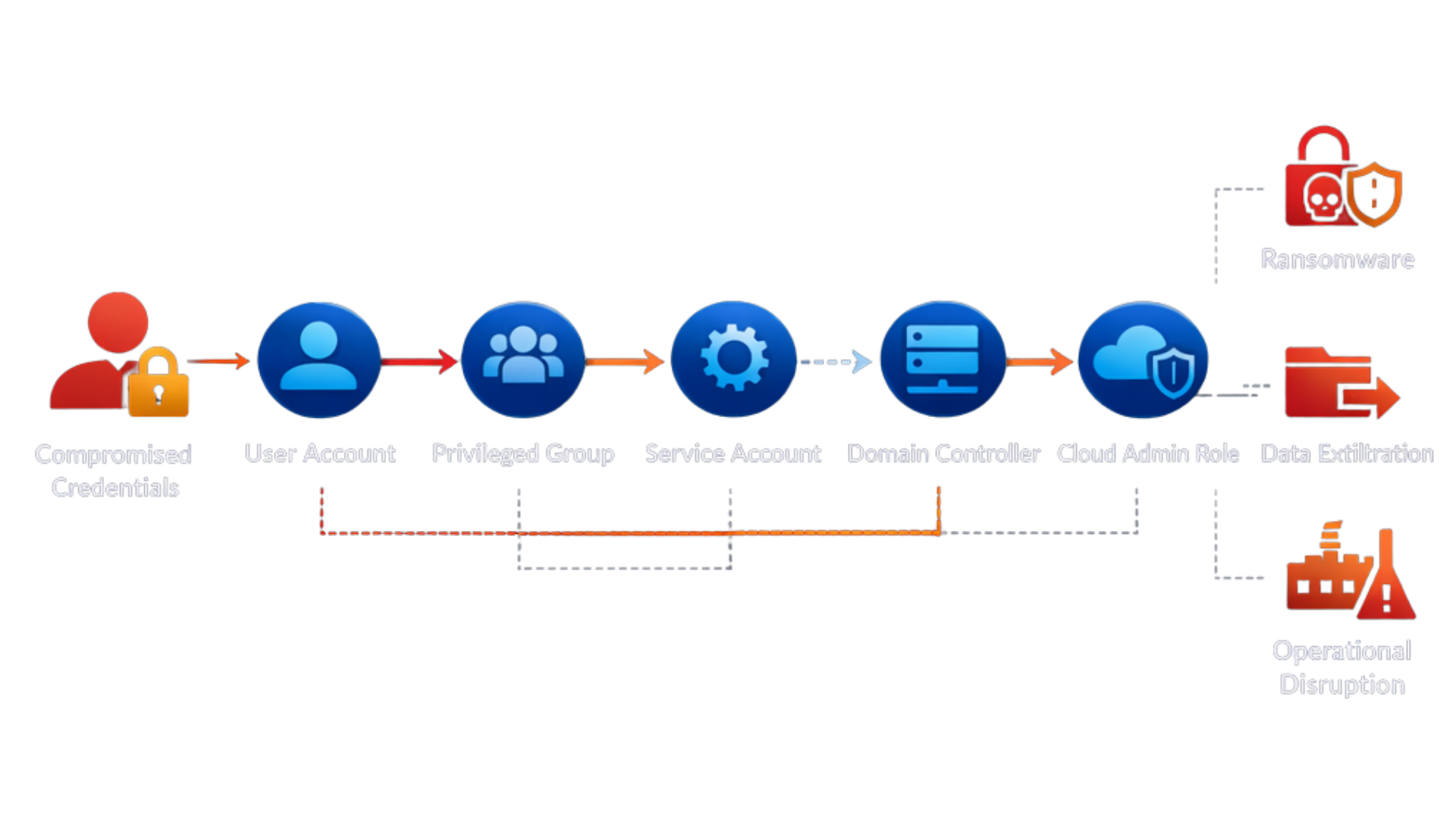
Breaches Start with Identity
Most breaches do not begin with malware.
They begin with identity misuse.
Compromised credentials.
Excessive privileges.
Unmonitored attack paths inside Active Directory and Microsoft Entra ID.
This is identity driven breach risk and it has quietly become the dominant attack surface for modern enterprises.
Firewalls are stronger.
Endpoint protection is smarter.
But identity remains structurally exposed.
What Is Identity Driven Breach Risk?
Identity driven breach risk refers to the likelihood that an attacker can exploit identity weaknesses to gain unauthorised access, escalate privileges, and move laterally across your environment.
Instead of breaking in, attackers log in.
Common identity-driven weaknesses include:
- Privilege sprawl across Active Directory
- Misconfigured roles in Microsoft Entra ID
- Dormant accounts with elevated access
- Weak MFA enforcement
- Unmonitored identity attack paths
Once identity is compromised, perimeter controls alone are insufficient.
Identity is the control plane of your organisation. When it fails, everything connected to it becomes reachable.
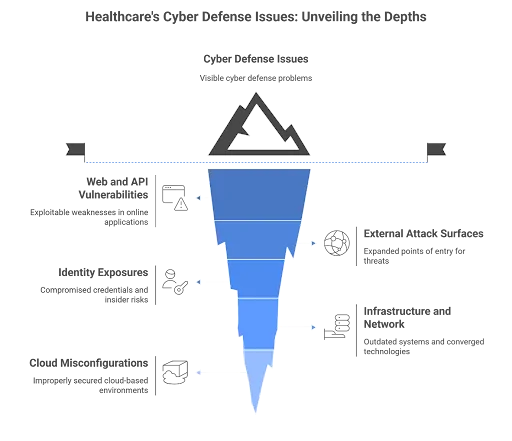
Why Identity Has Become the Primary Attack Surface
Modern infrastructure is identity-centric.
Cloud applications rely on federated authentication.
DevOps pipelines depend on service accounts.
Administrators operate across hybrid AD and Entra ID environments.
This creates three structural realities:
1. Identity Is Everywhere
Every user, service, workload, and integration depends on identity.
2. Privilege Accumulates Over Time
Role changes, temporary access, and legacy configurations create privilege creep.
3. Attack Paths Are Often Invisible
An attacker rarely needs a Domain Admin account immediately.
They follow identity relationships and escalate step by step.
Most organisations monitor alerts.
Few continuously validate identity exposure.
That gap is where identity driven breach risk grows.
Why Traditional Security Metrics Miss the Problem
Security dashboards often measure:
- Number of alerts
- Patch compliance
- Endpoint coverage
- MFA adoption rates
These metrics are important.
But they do not answer a more critical executive question:
How likely is it that an attacker can compromise identity and move laterally today?
Without understanding identity attack paths, organisations operate with false confidence.
Compliance does not equal resilience.
Tool deployment does not equal risk reduction.
Identity driven breach risk requires continuous measurement, not periodic audits.
The Business Impact of Identity-Driven Breaches
When identity is compromised:
- Ransomware spreads faster
- Recovery becomes complex
- Backup systems may be targeted
- Domain rebuilds can take weeks
Identity compromise often leads to operational paralysis, not just data exposure.
For CISOs and CIOs, the risk is no longer theoretical.
Board-level conversations are shifting toward:
- Recovery readiness
- Identity resilience
- Operational continuity
Understanding identity driven breach risk is now a strategic requirement, not a technical exercise.
The Strategic Shift: From Detection to Likelihood Reduction
The conversation must expand beyond detection to likelihood reduction.
Instead of asking:
“Can we detect an identity attack?”
The better question is:
“How likely is it that identity can be exploited in the first place?”
Reducing identity driven breach risk requires:
- Baseline visibility into identity attack paths
- Risk-based prioritisation of privilege exposure
- Continuous validation of remediation effectiveness
This is where proactive identity resilience replaces reactive security operations.
What Success Looks Like
Without action:
- Privilege escalation paths remain hidden
- Recovery plans go untested
- Identity compromise becomes a matter of time
With structured identity resilience:
- Breach likelihood decreases
- Attack paths are continuously reduced
- Recovery confidence increases
- Executive visibility improves
Identity is now the primary attack surface.
Managing it like a static directory service is no longer viable.
Understand Your Identity Breach Likelihood
If identity is your control plane, you need to understand its exposure.
A structured assessment can help quantify your current identity driven breach risk across Active Directory and Microsoft Entra ID, identify attack paths, and prioritise remediation.
Start with a Breach Likelihood Assessment.
Reduce identity-driven breach risk before attackers exploit it.