Stay Ahead of the Curve with
Real-World Cyber Insights
80% of breaches start with poor identity hygiene.
60% of mid-sized organisations lack visibility into exposed assets.
90% of security teams say they’re stuck reacting instead of preventing.
They trusted in us










Datasheets & Service Overview
Quick summaries of our offerings to help you understand how we can help.
Risk-to-Resilience Exposure Management Datasheet
A quick overview of our expert-led approach to uncover, prioritise, and fix cyber exposures.
Risk-to-Resilience Managed Exposure Program
Explore our structured, outcome-based program with monthly reporting and a 90-day guarantee.
Managed Identity Resilience (MIR) Service
Explore how MIR helps organisations reduce identity breach likelihood with managed identity protection and continuous risk reduction.
Managed Cloud Resilience (MCR) Service
Explore how MCR helps organisations reduce exploitable cloud breach risk through continuous visibility, prioritisation, and engineering-led remediation across multi-cloud environments.
Ready to Move from Risk to Resilience?
Take the first step with a complimentary baseline assessment
Latest Blogs

Cloud Exposure Is Growing Faster Than Security Teams Can Track
Cloud environments change faster than many security teams can track. Learn why cloud exposure management is becoming essential for reducing modern attack surface risk.

Why Identity Security Recovery Fails
Identity recovery readiness is often overlooked until identity systems are compromised. Learn why recovery fails and how security teams can improve resilience.
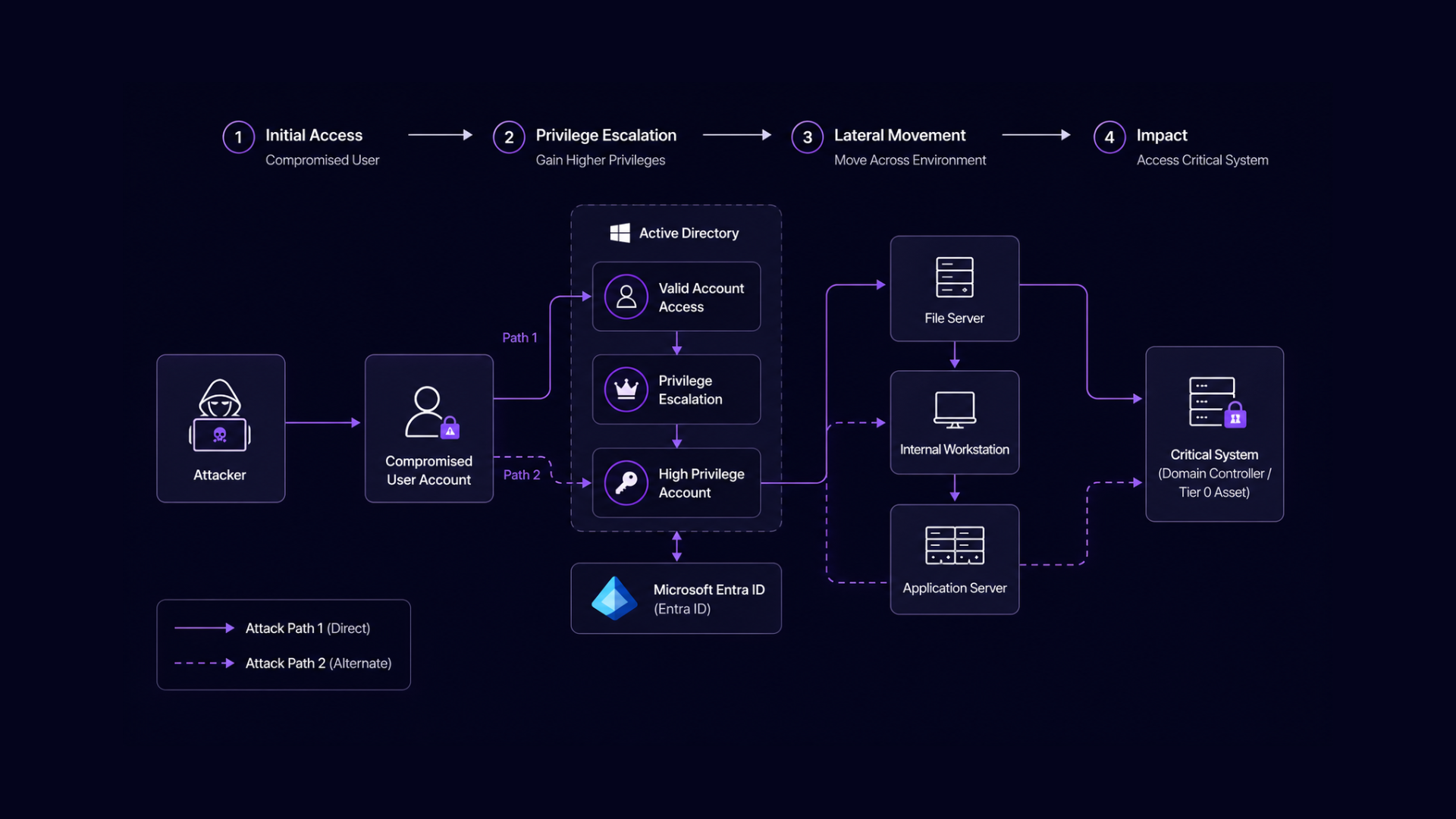
5 Identity Attack Paths You Haven’t Tested
Most breaches follow hidden identity attack paths. Learn the 5 paths security teams rarely test and how to uncover them before attackers do.
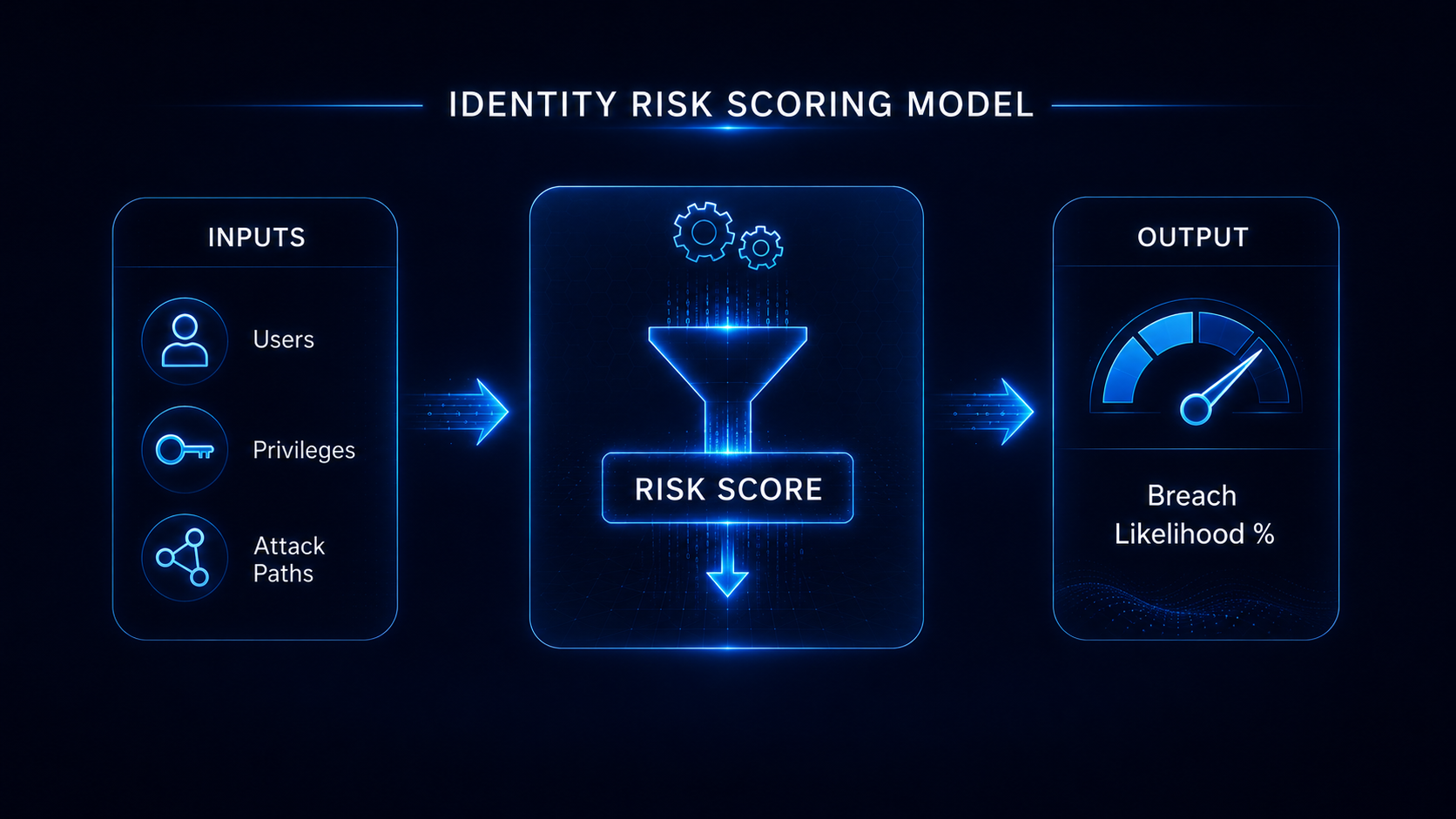
Measure Your Identity Breach Risk in 30 Days
A breach likelihood assessment helps organisations measure identity risk across Active Directory and Entra ID. Learn how to identify exposure and reduce breach likelihood in 30 days.

Microsoft Entra ID Misconfigurations CISOs Miss
Entra ID security gaps are often caused by overlooked misconfigurations and identity exposure. Learn how these gaps increase the likelihood of identity-driven breaches.

Active Directory Is Still Your Biggest Security Risk
Active Directory security risks remain one of the most overlooked threats in enterprise security. Learn how AD attack paths and privilege escalation expose organisations to identity-driven breaches.
