Active Directory Still Sits at the Center of Most Breaches
Despite years of security investment, Active Directory remains one of the most common entry points for enterprise attacks.
Most organisations believe their perimeter security is the primary defence.
But attackers rarely need to break through the perimeter anymore.
Instead, they exploit identity weaknesses inside Active Directory, following privilege relationships and hidden attack paths to escalate access.
For many enterprises, the risk is not that Active Directory will be attacked.
It is that it has already become the easiest path to full domain compromise.
Why Active Directory Security Risks Continue to Grow
Active Directory was designed for a very different era of enterprise computing.
Originally built to manage authentication and access inside trusted internal networks, it now operates inside hybrid environments connected to cloud services, applications, and remote workforces.
This expansion has significantly increased the number of identity relationships inside the environment.
Common sources of Active Directory security risks include:
- Privilege sprawl across administrative groups
- Legacy service accounts with excessive permissions
- Dormant privileged accounts that remain active
- Weak segmentation between administrative tiers
- Poor visibility into identity attack paths
Over time, these relationships create complex privilege chains that attackers can exploit.
What appears to be a minor misconfiguration can become a critical escalation path.
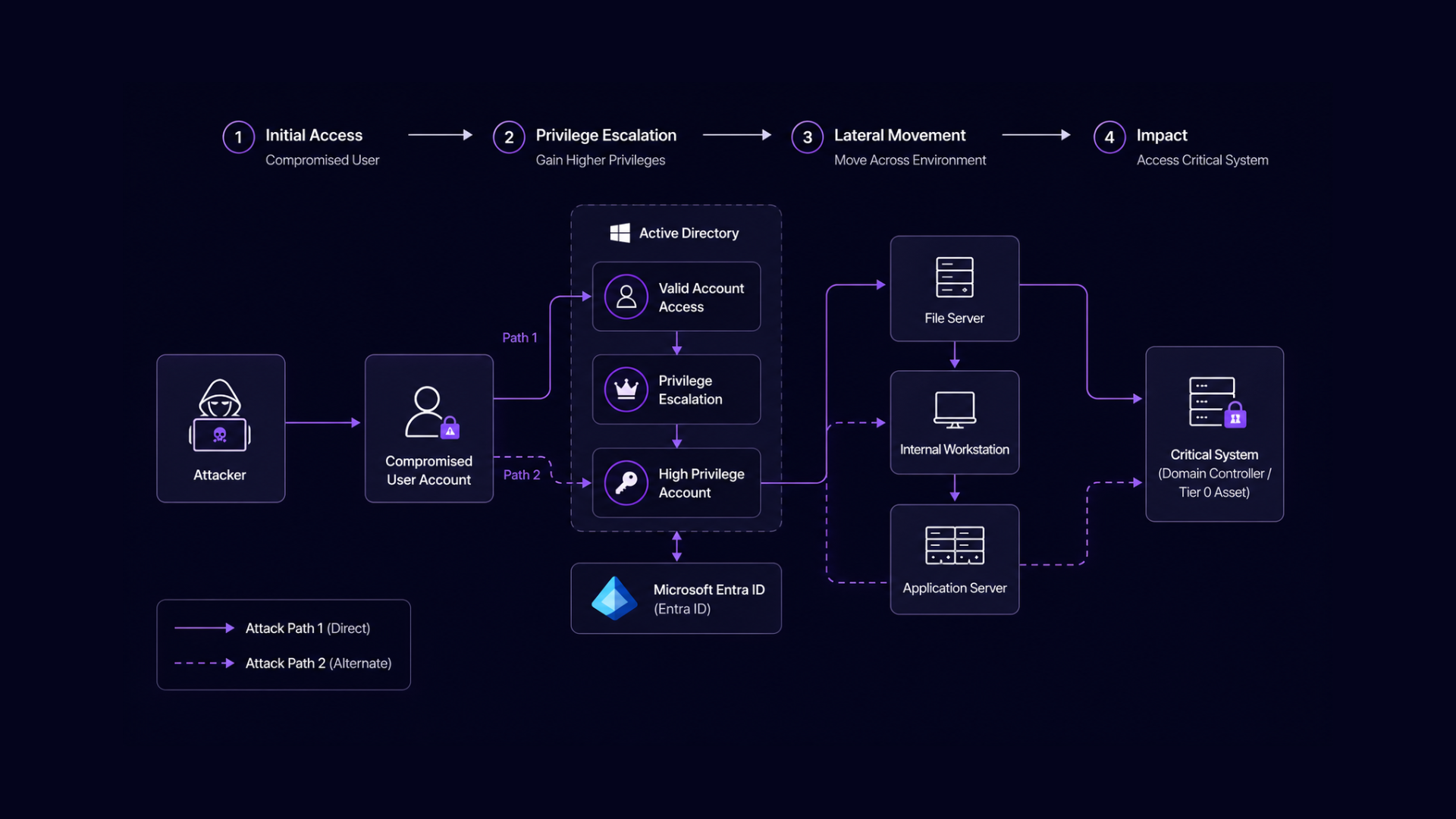
How Attackers Exploit AD Attack Paths
Modern attackers rarely aim directly for Domain Admin access.
Instead, they move gradually through the environment by abusing identity relationships.

This technique is known as attack path escalation.
An attacker may start with a compromised user account and then identify a sequence of privilege relationships such as:
User Account → Privileged Group → Service Account → Domain Controller
Each step increases access until the attacker reaches a position of full control.
These AD attack paths often exist for years without detection because traditional security tools focus on alerts rather than privilege relationships.
As a result, organisations may have strong monitoring but still carry significant identity exposure.
Privilege Escalation Is Often Invisible
One of the most dangerous aspects of Active Directory security risks is how quietly privilege escalation can occur.
Many escalation techniques do not require malware.
Attackers simply leverage existing identity relationships and administrative permissions.
Examples include:
- Kerberoasting to extract service account credentials
- Abuse of delegated permissions
- Token impersonation and credential reuse
- Misconfigured group memberships
Each of these techniques enables attackers to move laterally without triggering traditional security alarms.
In many real-world breaches, escalation occurs slowly over days or weeks.
By the time detection occurs, attackers may already control the domain.
Why Many Security Programs Miss AD Exposure
Security teams often believe Active Directory is secure because:
- MFA is enabled
- Endpoint protection is deployed
- Monitoring tools are active
These controls are valuable, but they do not eliminate identity attack paths.
Most organisations lack continuous visibility into:
- Privilege relationships across AD
- Identity exposure between systems
- Escalation paths connecting accounts and resources
Without understanding these relationships, Active Directory security risks remain hidden inside the environment.
Compliance checks may pass.
But the underlying identity exposure still exists.
Reducing Active Directory Security Risk
Reducing exposure requires shifting from reactive monitoring to proactive identity resilience.
Security teams must continuously analyse identity relationships to identify escalation paths before attackers exploit them.
This includes:
- Mapping privilege relationships across the environment
- Identifying high-risk escalation paths
- Reducing unnecessary privileges
- Validating identity resilience continuously
By focusing on attack path reduction, organisations can significantly decrease the likelihood of identity-driven breaches.
Active Directory Risk Is Ultimately a Business Risk
When Active Directory is compromised, the impact is rarely limited to IT systems.
Identity compromise can lead to:
- Domain takeover
- Ransomware propagation
- Data exfiltration
- Operational disruption
Because Active Directory sits at the center of enterprise authentication, its security posture directly affects organisational resilience.
Understanding and reducing Active Directory security risks is therefore not just a technical task.
It is a strategic requirement for modern security programs.
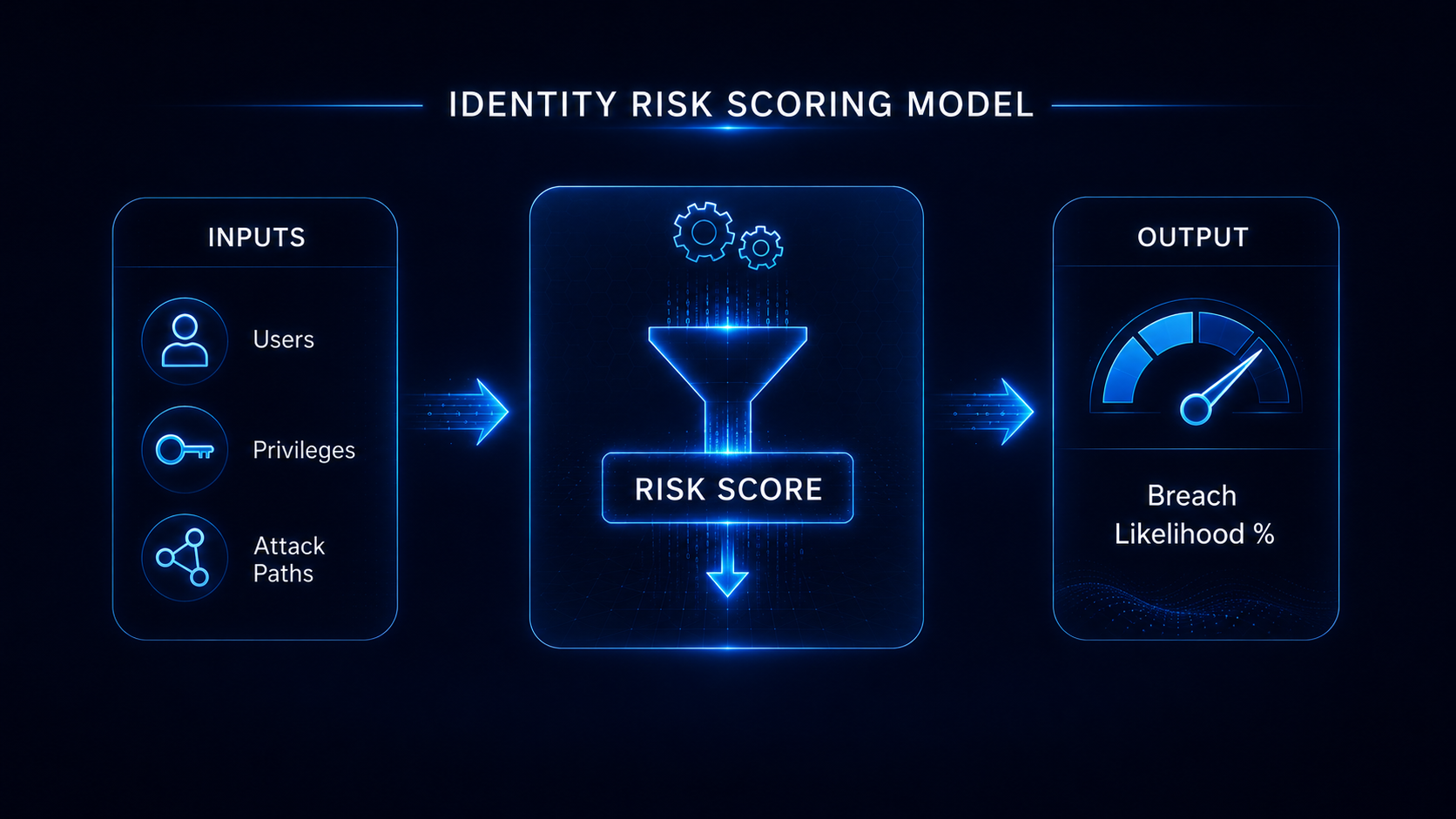
Understand Your Identity Breach Likelihood
Identity compromise often begins with hidden exposure inside Active Directory.
A structured Breach Likelihood Assessment can help identify identity attack paths, privilege escalation risks, and configuration weaknesses across Active Directory and Microsoft Entra ID.
Understanding your exposure is the first step toward reducing identity-driven breach risk.