Identity Risk Is Measurable, But Often Not Measured
Most organisations understand that identity is the primary attack path.
But very few can answer a simple question:
How likely are we to experience an identity-driven breach today?
Security programs often focus on tools, alerts, and compliance.
But they rarely provide a clear, measurable view of identity risk.
Without this, organisations operate without understanding their true exposure.
Why Traditional Security Metrics Fall Short
Many security teams rely on metrics such as:
- Number of alerts
- Vulnerabilities patched
- MFA adoption rates
- Compliance scores
While useful, these do not measure real breach likelihood.
They do not show:
- Whether attack paths exist
- How privilege escalation could occur
- How identities connect across systems
This creates a gap between perceived security and actual identity-driven breach risk.
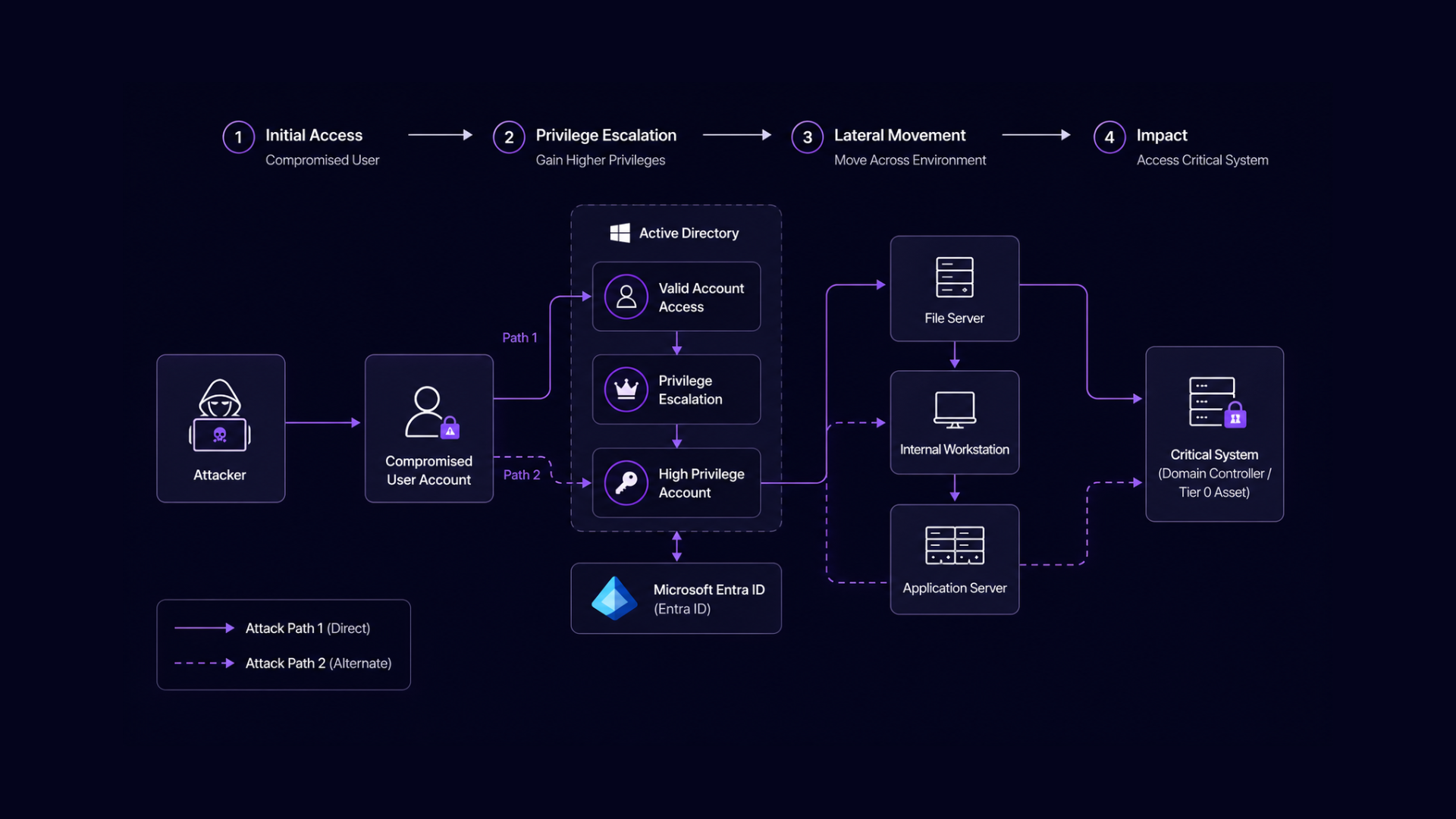
What a Breach Likelihood Assessment Actually Measures
A breach likelihood assessment focuses on identity relationships rather than isolated controls.
It evaluates:
- Attack paths across Active Directory and Entra ID
- Privilege escalation opportunities
- Identity misconfigurations and exposure
- Lateral movement potential across environments
Many of these exposures originate from existing Active Directory security risks that are not fully understood.
Instead of asking “Are controls in place?”
It asks:
“Can an attacker reach critical systems using existing identities?”
This shift changes how risk is understood.
In cloud environments, this is often driven by Entra ID security gaps and misconfigurations.
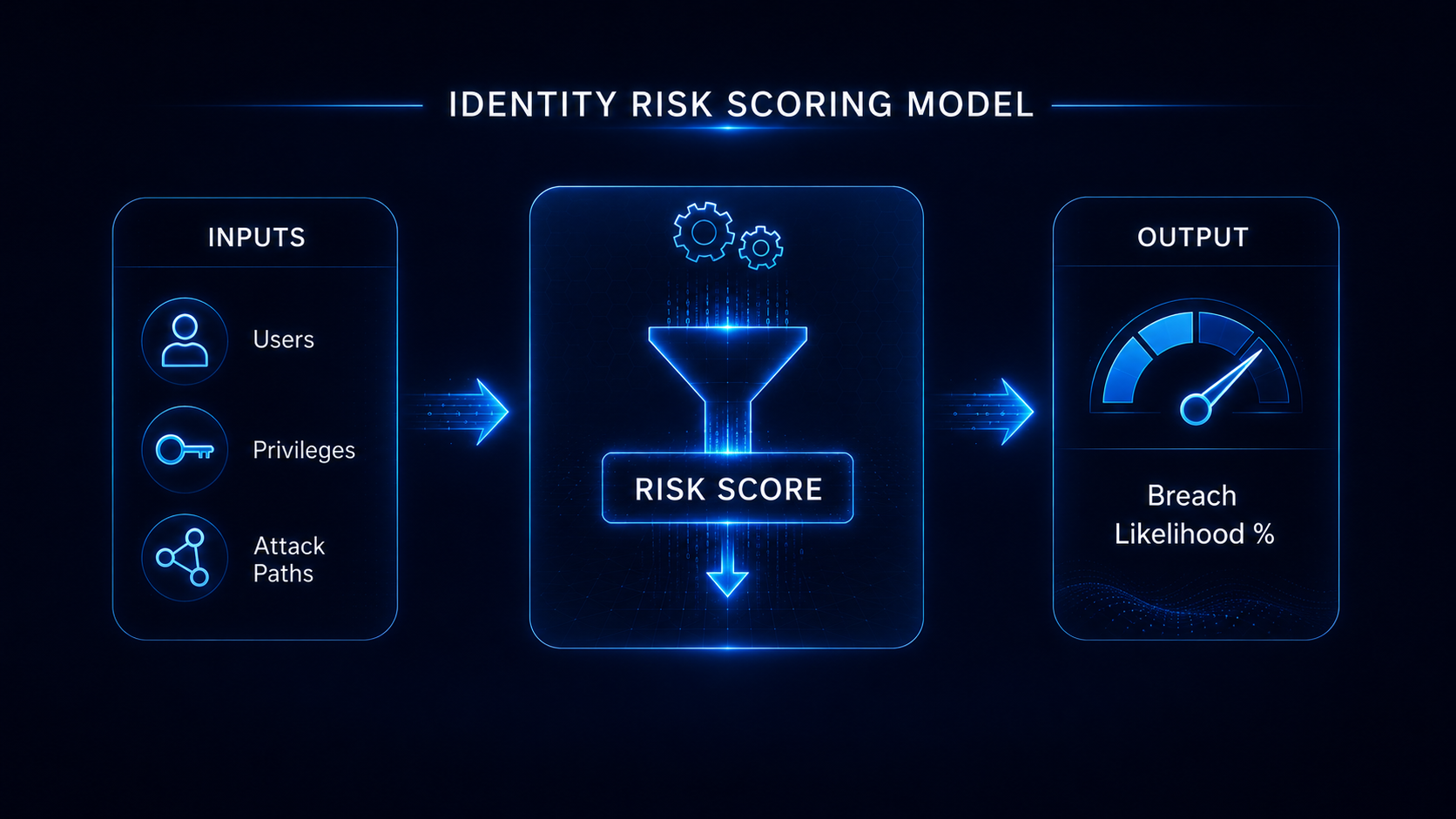
How Identity Breach Likelihood Is Calculated
A structured assessment typically follows four key steps:
1. Identity Discovery
Map users, service accounts, roles, and permissions across environments.
2. Attack Path Analysis
Identify how identities connect and where escalation paths exist.
3. Risk Prioritisation
Focus on high-impact paths that lead to critical assets.
4. Exposure Scoring
Quantify the likelihood of breach based on real attack paths.
This approach transforms identity risk into something measurable and actionable.
Why 30 Days Is Enough to Gain Clarity
Many organisations assume this level of analysis takes months.
It doesn’t.
With the right approach, a breach likelihood assessment can be completed in as little as 30 days.
This is possible because:
- Data is collected through read-only integrations
- Analysis focuses on identity relationships, not full infrastructure
- Risk is prioritised based on impact, not volume
Within weeks, organisations gain visibility into risks that may have existed for years.
Where Most Assessments Fail
Many organisations attempt to assess identity risk internally.
Common challenges include:
- Limited visibility into identity relationships
- Lack of tooling to map attack paths
- Difficulty prioritising remediation
- Resource constraints within security teams
As a result, assessments often become:
- One-time exercises
- Incomplete analyses
- Reports without actionable outcomes
This limits their effectiveness.
From Assessment to Continuous Identity Resilience
Measuring breach likelihood is only the first step.
Reducing it requires continuous effort.
This includes:
- Ongoing monitoring of identity exposure
- Continuous identification of new attack paths
- Guided remediation of high-risk issues
- Validation of security posture over time
Without this, risk begins to accumulate again.
How Organisations Operationalise This
Leading organisations move from periodic assessments to continuous identity resilience programs.
This allows them to:
- Maintain visibility into identity risk
- Reduce exposure proactively
- Respond to emerging threats faster
- Align security efforts with measurable outcomes
This is where managed approaches become critical.
A Practical Approach to Reducing Breach Likelihood
A structured Breach Likelihood Assessment provides a starting point.
But the real value comes from:
- Continuous detection of identity exposure
- Prioritised remediation support
- Ongoing validation of identity resilience
This is the approach behind Managed Identity Resilience (MIR).
Rather than relying on internal resources and tools, organisations adopt a fully managed capability that continuously reduces identity breach likelihood.
Understand Your Identity Risk in 30 Days
Identity risk does not need to remain abstract.
A breach likelihood assessment provides a clear, measurable view of exposure across Active Directory and Entra ID.
From there, organisations can take structured steps to reduce risk and strengthen identity resilience.