Entra ID Has Expanded the Identity Attack Surface
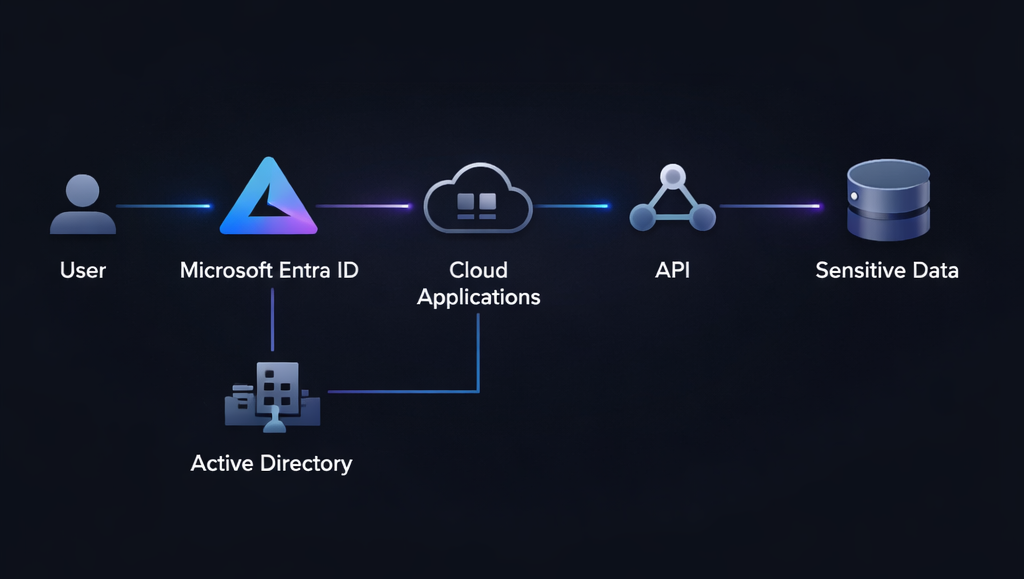
As organisations adopt cloud and hybrid environments, Microsoft Entra ID has become central to authentication and access management.
It connects users to applications, cloud services, and external identities.
This centralisation improves flexibility.
But it also introduces new layers of complexity.
Most organisations assume their Entra ID environment is secure because baseline controls such as MFA are enabled.
However, Entra ID security gaps often exist beneath these controls, hidden within configuration settings, permissions, and identity relationships.
Why Entra ID Security Gaps Are Often Overlooked
Unlike traditional infrastructure, Entra ID is highly dynamic.
Changes happen continuously:
- New applications are integrated
- Permissions are granted and modified
- External identities are added
- Conditional access policies evolve
Over time, these changes create configuration drift.
What begins as a secure setup gradually becomes misaligned with security best practices.
Common sources of Entra ID security gaps include:
- Overly permissive application registrations
- Weak or inconsistent conditional access policies
- Excessive delegated permissions
- Unmonitored guest accounts
- Legacy authentication still enabled
Individually, these may appear low risk.
Collectively, they form exploitable identity exposure.
How Misconfigurations Create Identity Exposure
Attackers do not need to exploit vulnerabilities in code.
They exploit misconfigurations in identity systems.
For example:
- An application with excessive API permissions
- A user with unnecessary administrative roles
- A conditional access policy that excludes certain scenarios
These gaps create opportunities for attackers to move across identities and services.
Unlike traditional attacks, these movements often rely on legitimate access paths.
This makes detection significantly more difficult.
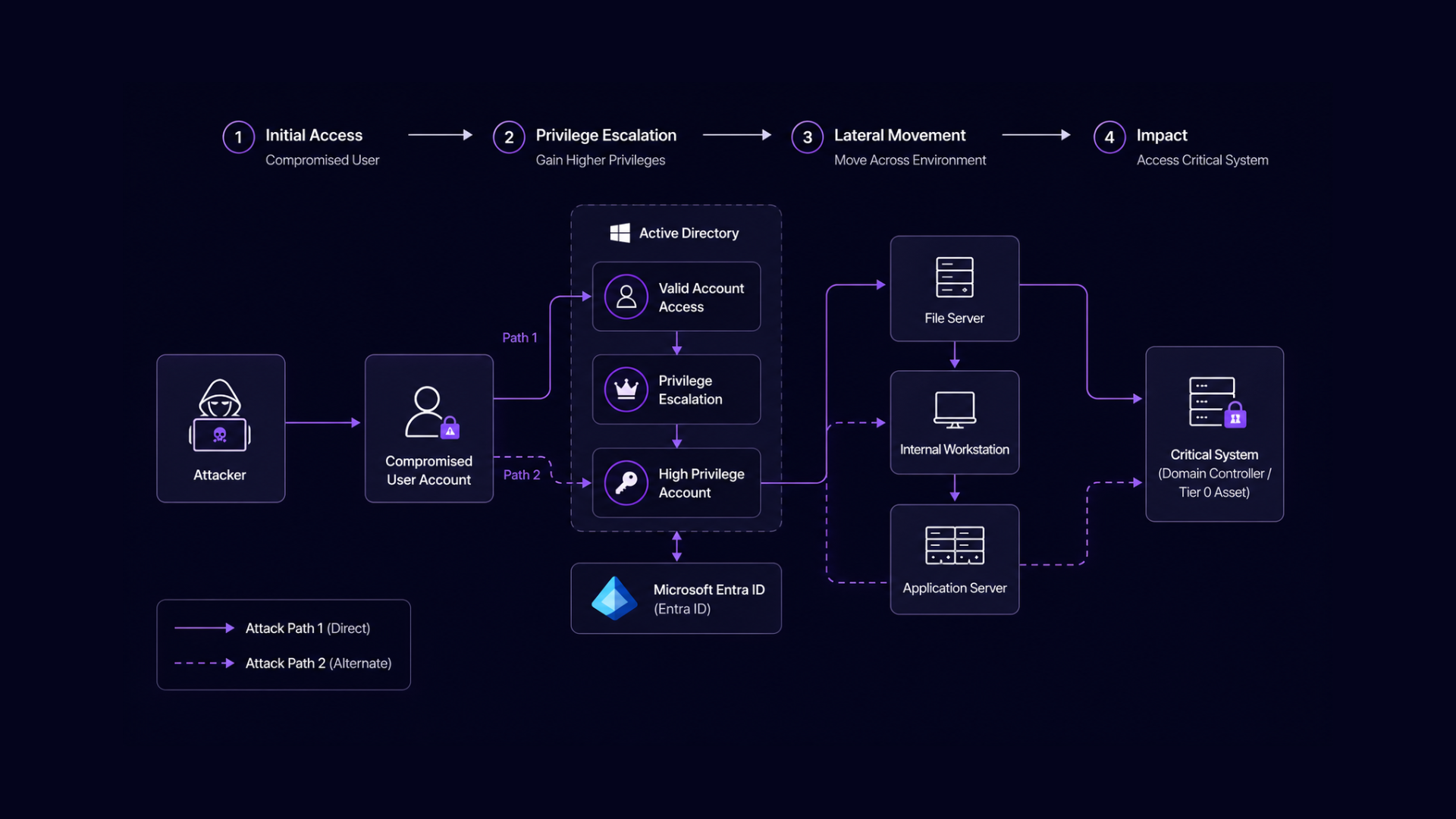
Entra ID Security Gaps Enable Privilege Escalation
Once an attacker gains initial access, Entra ID security gaps can enable rapid escalation.
Examples include:
- Assigning roles through compromised accounts
- Leveraging application permissions to access data
- Abusing token-based authentication flows
- Exploiting weak conditional access enforcement
These escalation paths may not trigger alerts because they operate within expected system behaviour.
As a result, attackers can expand access while remaining undetected.
Visibility Is the Core Challenge
Most organisations lack continuous visibility into:
- Identity relationships across Entra ID
- Permission dependencies between users and applications
- Policy gaps in conditional access
- Exposure created by external identities
Security tools often focus on events rather than relationships.
This creates a blind spot.
Without visibility into how identities connect, Entra ID security gaps remain hidden until they are exploited.
Reducing Entra ID Security Gaps
Closing these gaps requires a shift from static configuration reviews to continuous identity exposure management.
This involves:
- Monitoring configuration drift over time
- Analysing permission structures across users and applications
- Identifying high-risk identity relationships
- Validating conditional access policies against real-world scenarios
By continuously assessing identity exposure, organisations can reduce the likelihood of misconfiguration-driven breaches.
Entra ID Risk Extends Beyond the Cloud
Although Entra ID operates in the cloud, its impact extends across the entire enterprise.
It integrates with Active Directory, which continues to carry significant Active Directory security risks, as well as SaaS applications, third-party platforms, and external partners.
This means that Entra ID security gaps can amplify risk across hybrid environments.
A single misconfiguration can expose multiple systems.
Connecting Entra ID Risk to Identity-Driven Breaches
Identity exposure in Entra ID is not isolated.
It often connects directly to broader identity-driven breach risk across the organisation.
Misconfigurations in Entra ID can:
- Enable lateral movement between cloud and on-prem environments
- Expand attack paths beyond traditional boundaries
- Increase the likelihood of privilege escalation
Understanding these relationships is critical for modern security programs.
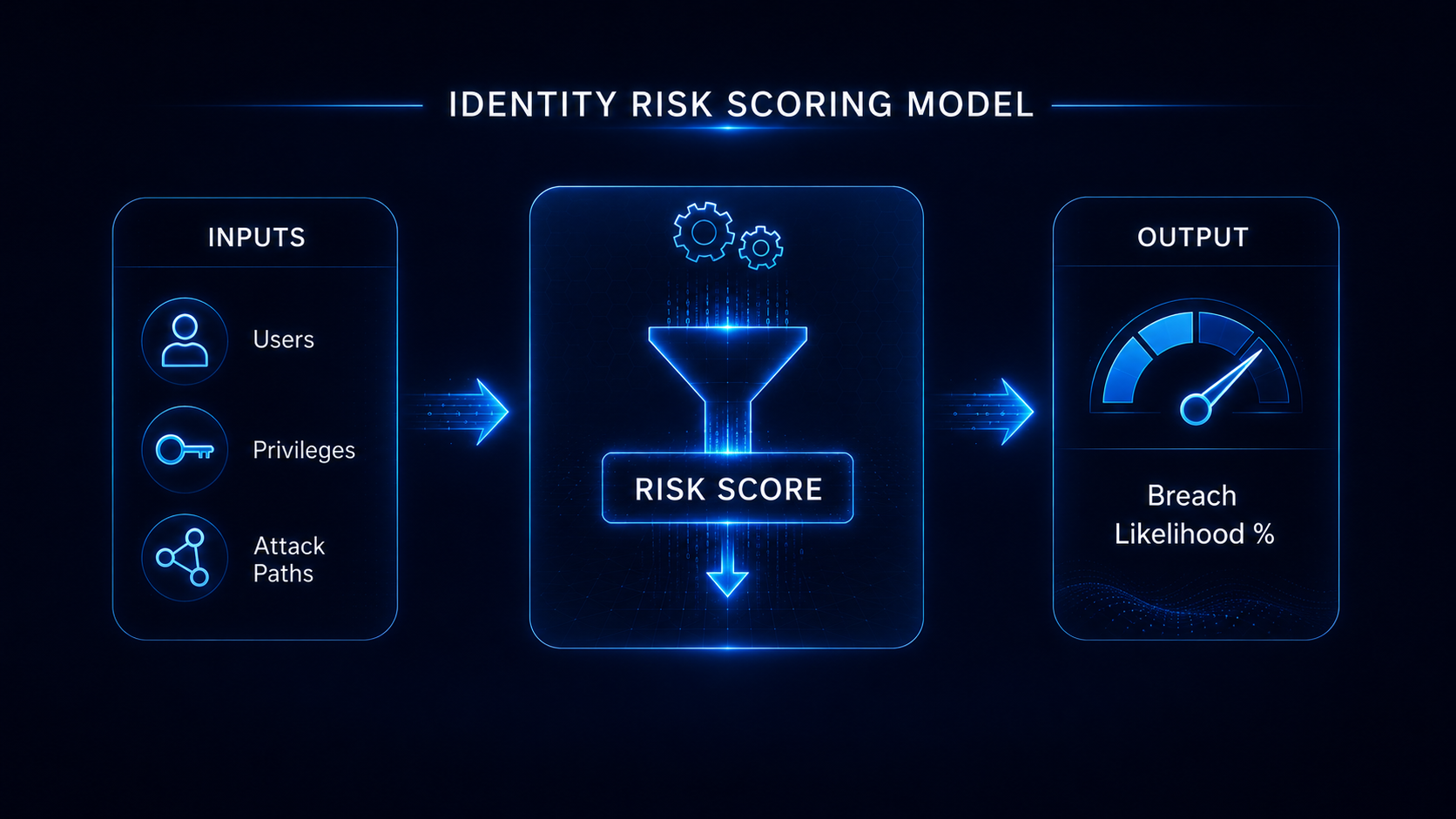
Understand Your Identity Exposure
Entra ID security gaps often remain invisible without structured analysis.
A Breach Likelihood Assessment can identify misconfigurations, privilege exposure, and identity attack paths across Microsoft Entra ID and Active Directory.
Understanding your exposure is the first step toward reducing identity-driven breach risk.