Most security teams focus on alerts, tools, and patching.
But attackers don’t think in tools.
They think in paths.
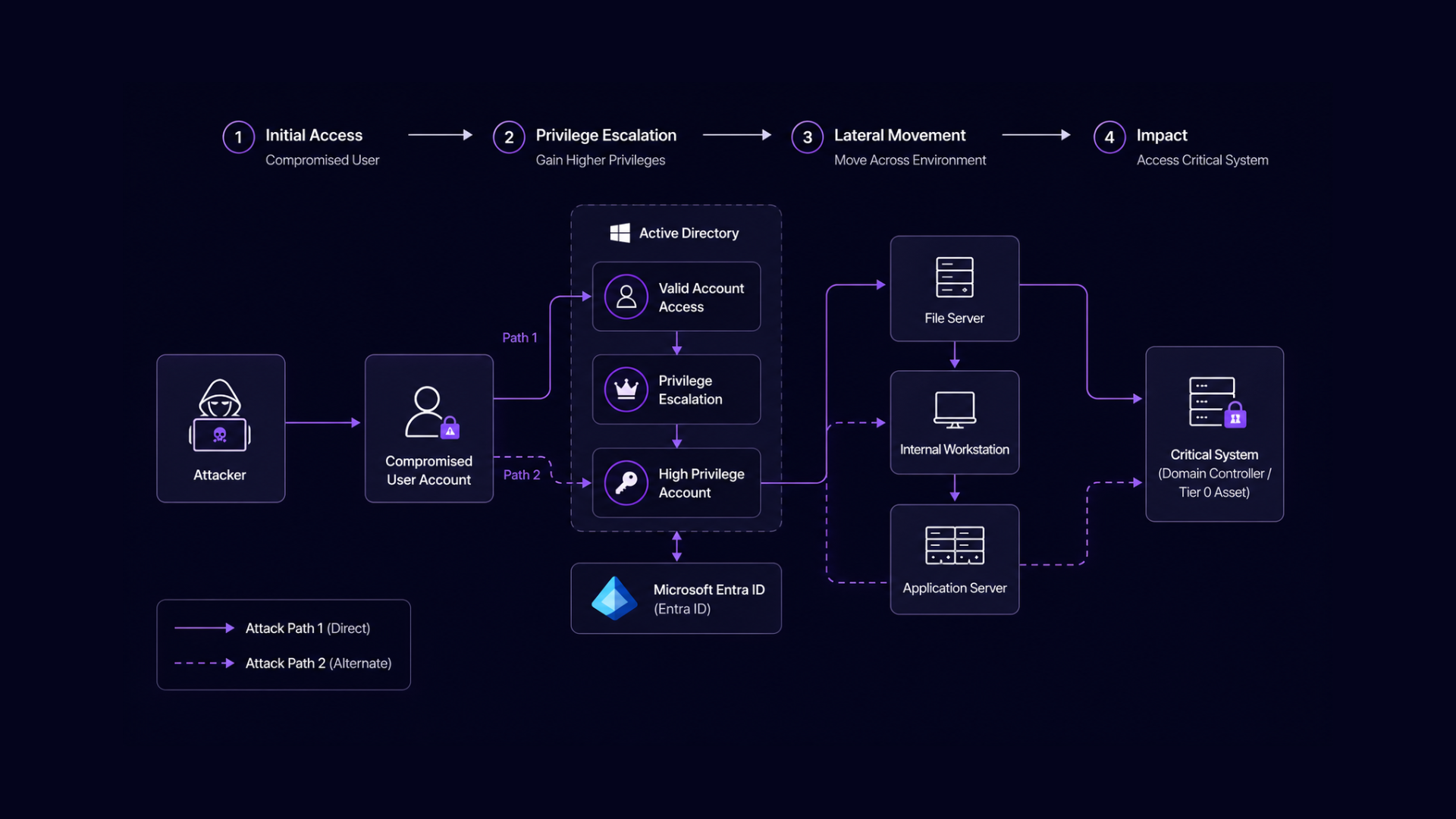
An identity attack path is the sequence of steps an attacker can take using valid access, misconfigurations, and privilege escalation to reach critical systems.
The problem?
Most of these paths are never tested.
What Are Identity Attack Paths?
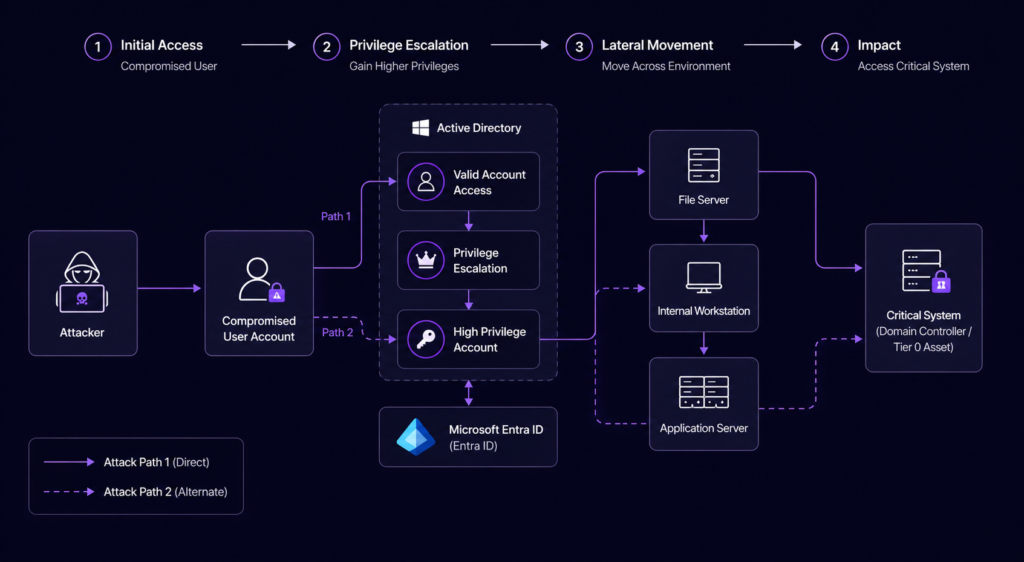
Identity attack paths are hidden routes inside your environment.
They connect:
- Users
- Privileges
- Misconfigurations
- Systems
Attackers don’t need malware if these paths already exist.
They move quietly using:
- Legitimate credentials
- Over-permissioned accounts
- Weak configurations
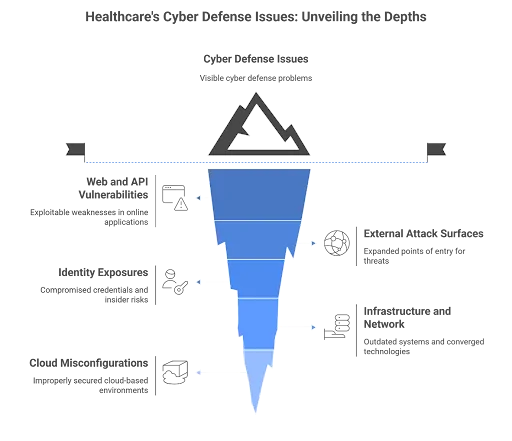
Why Most Organizations Miss Them
Security tools show alerts.
Attack paths show how a breach actually happens.
The gap:
- Alerts = point-in-time
- Attack paths = full journey
Without visibility into identity attack paths:
- You don’t see lateral movement risk
- You don’t understand privilege chaining
- You can’t prioritize what actually matters
- You remain exposed to underlying Active Directory security risks that enable these paths
The 5 Identity Attack Paths You Probably Haven’t Tested
1. Dormant Privileged Accounts
Old admin accounts that were never removed.
They often:
- Have high privileges
- Lack monitoring
- Bypass modern controls
Attackers love them because no one is watching.
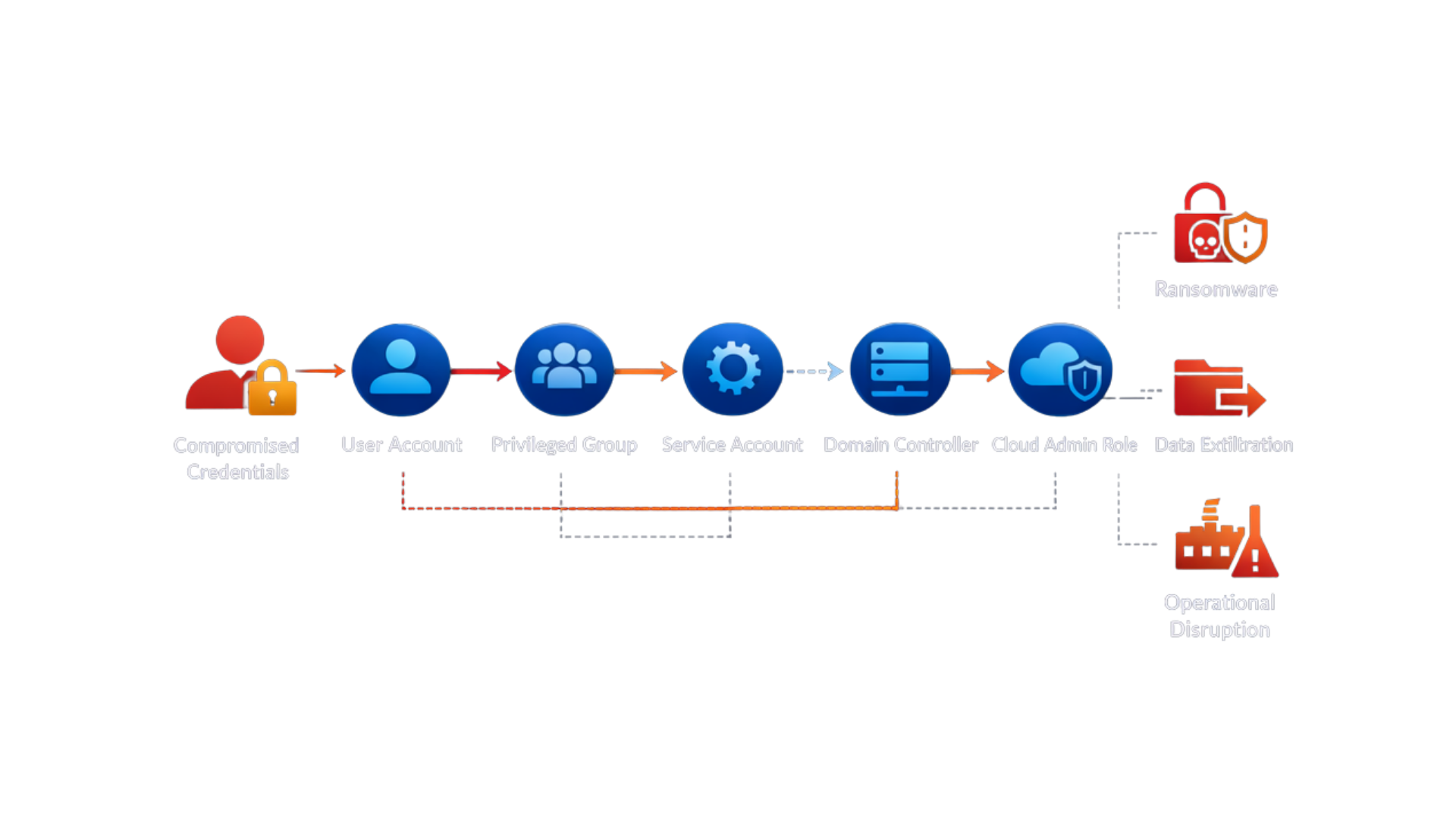
2. Service Account Over-Permissioning
Service accounts are rarely cleaned up.
Common issues:
- Excessive permissions
- No MFA
- Hardcoded credentials
One compromised service account can open multiple systems.
3. Token Abuse in Entra ID
Modern attacks don’t always rely on passwords.
Many of these risks come from overlooked Entra ID security gaps that attackers quietly exploit.
Attackers can:
- Steal tokens
- Reuse sessions
- Bypass MFA
This creates silent persistence inside your environment.
4. Privilege Escalation Chains
Low-level access can become admin access.
Example path:
User → Group → Application → Admin Role
These chains are often invisible without mapping.
5. Hybrid Identity Gaps (AD + Entra ID)
Most environments are hybrid.
Risk appears when:
- Permissions don’t align
- Sync configurations are weak
- Policies differ across systems
Attackers move between AD and Entra ID to escalate access.
Why Testing These Paths Changes Everything
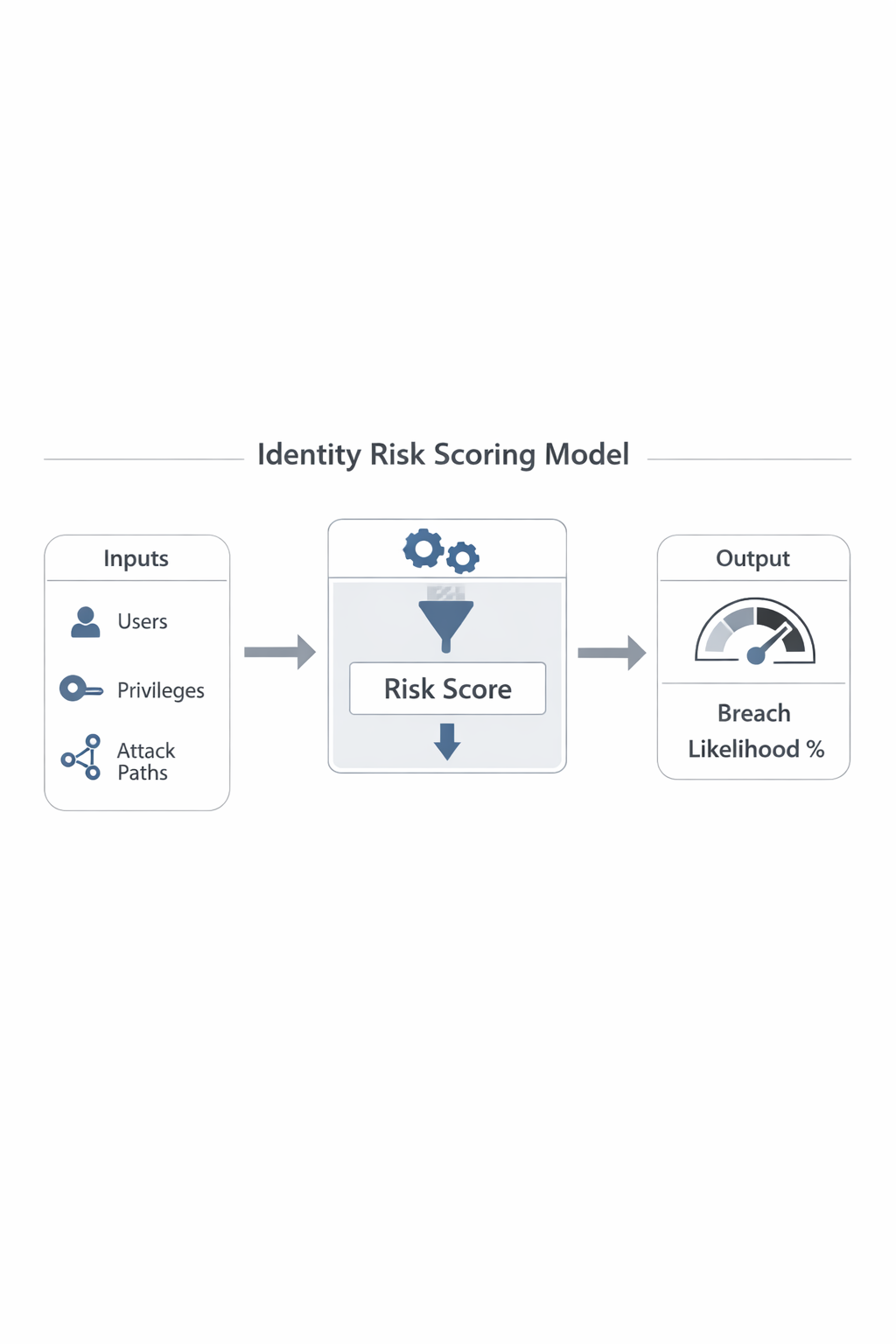
When you test identity attack paths:
- You see real exposure, not assumptions
- You prioritize based on risk, not noise
- You fix root causes, not symptoms
This is how you move from reactive to proactive security.
How to Actually Validate Your Exposure
You don’t need another tool.
You need:
- Visibility into identity relationships
- Continuous validation of attack paths
- Clear prioritization of what to fix
This is exactly what a
👉 breach likelihood assessment
is designed to do.